Your marketing team created a compelling patient success story. A local patient enthusiastically agreed to share their recovery journey from knee surgery. The post is ready to go live across all your social media platforms, and you’re confident it will drive patient inquiries. Then your compliance officer flags a critical problem: the patient’s written authorization specifies only Facebook use, not Instagram. The post cannot go live as planned.
This scenario repeats across healthcare organizations constantly. HIPAA violations occur not from intentional misconduct, but from systematic gaps in authorization procedures, inadequate content review processes, and insufficient staff training on what constitutes protected health information. Organizations understand HIPAA applies to medical records and patient interactions, yet many fail to recognize that social media demands equally rigorous compliance standards.
A single unreviewed post exposing protected health information can trigger federal investigations by the Office for Civil Rights (OCR), financial penalties exceeding $50,000 per violation, mandatory patient notifications, media disclosure, and reputational damage that persists for years. Yet these violations are entirely preventable through structured compliance processes.
This blog explains the most common HIPAA violations healthcare organizations make on social media. Learn the root causes of these breaches, understand why well-intentioned teams inadvertently violate federal law, and discover proven steps to implement compliance safeguards that transform social media from a compliance risk into a strategic asset.
Understanding HIPAA Requirements for Healthcare Social Media
HIPAA (Health Insurance Portability and Accountability Act) is a federal law enacted in 1996 to protect patient privacy and establish national standards for healthcare data security. While most healthcare professionals understand HIPAA applies to medical records and patient interactions, many fail to recognize that HIPAA protections extend to social media platforms equally.
What Counts as Protected Health Information (PHI)?
PHI includes any individually identifiable health information that healthcare organizations maintain in any form, paper, electronic, or digital. On social media, PHI includes:
- Patient Names: Even naming a patient in a post without additional health information constitutes PHI.
- Medical Conditions and Diagnoses: Mentioning specific diseases, treatments, or surgical procedures.
- Dates of Service: Specific admission dates, appointment times, or treatment timelines tied to identifiable individuals
- Photos and Images: Visual identification of patients, even without names attached
- Patient Age and Demographics: Age combined with diagnosis or location often identifies individuals.
- Treatment Details and Outcomes: Describing specific procedures, medications, or recovery milestones.
- Medical Record Numbers: Any unique identifiers connected to patient records.
- Location Information: Specific departments, facilities, or hospital locations combined with patient information.
The critical distinction is that HIPAA protects information that could reasonably identify an individual. A post about “a 45-year-old man recovering from heart surgery at our downtown campus” may not contain a name, but the combination of age, condition, treatment, and location likely identifies a specific patient. HIPAA violations occur not only when names are published but whenever a reasonable person could identify the patient from the combined information presented.
Key HIPAA Social Media Regulations
The HIPAA Privacy Rule (45 CFR Part 164) establishes that healthcare providers can only use or disclose PHI under specific circumstances:
- Patient Authorization: Written authorization from the patient is required before any PHI disclosure on social media. Generic consent forms are insufficient; specific written permission for social media use must exist.
- Minimum Necessary Standard: When sharing patient information is authorized, healthcare providers must limit disclosure to only the minimum information necessary to achieve the intended purpose.
- Business Associate Requirements: If social media platforms or third-party management tools process patient data, they must have Business Associate Agreements (BAAs) in place.
- No Assumption of Consent: Patient consent for treatment does not imply consent for social media use. Separate, documented authorization specifically for social media publication is required.
- Breach Notification Obligations: When HIPAA violations occur, OCR requires notification to affected patients, media outlets, and law enforcement within 60 days.
Seven Common HIPAA Violations Healthcare Organizations Make on Social Media
Understanding where compliance typically breaks down helps prevent costly mistakes. These seven violations account for the majority of healthcare social media HIPAA enforcement actions.
1. Posting Patient Photos Without Written Authorization
Healthcare organizations frequently assume that verbal patient permission to take a photo is equivalent to HIPAA authorization for social media use. This fundamental misunderstanding leads directly to violations. A patient may cheerfully agree, “Sure, take a photo,” meaning permission for their hospital chart, not for publication to thousands of people on Facebook.
The Violation: Posting patient photos publicly without documented written authorization for that specific use.
Why It Happens: Healthcare staff move quickly during patient interactions. Verbal agreements seem sufficient in the moment. The authorization documentation process feels cumbersome compared to immediately snapping photos for social media.
Prevention:
- Implement mandatory written authorization forms specific to social media photography.
- The form must explicitly state that the photo will be shared on named social media platforms to the public.
- Verbal permission is insufficient; written documentation is non-negotiable.
2. Including Identifiable Information in Patient Success Stories
Patient testimonials drive engagement on healthcare social media. However, the details that make stories compelling (“Jane, a 47-year-old mother of three from the Westside neighborhood, overcame her decade-long battle with chronic migraines through our specialized pain management program”) often contain enough personal identifiers to violate HIPAA.
The Violation: Sharing enough identifying information that a reasonable person could connect the story to a specific individual.
Why It Happens: Compelling stories require detail and context. Removing identifying information often removes the emotional resonance that makes stories valuable. Teams find themselves caught between compliance and marketing effectiveness.
Prevention:
- Use de-identification techniques before publishing.
- The HIPAA Safe Harbor Method allows organizations to remove 18 specific identifiers and safely share patient information.
- Focus storytelling on the transformation and treatment experience rather than personally identifying details.
3. Failing to Obtain Specific Written Authorization
Generic patient consent forms that say “I consent to treatment and privacy practices” do not constitute social media authorization under HIPAA. OCR enforcement actions frequently find that healthcare organizations had some form of patient consent on file, but that the consent did not specifically mention social media use or named platforms.
The Violation: Assuming general healthcare consent covers social media publication without specific documented authorization for that use.
Why It Happens: Centralized patient intake processes create consent documents that cover treatment authorization and privacy practices. Assuming these blanket consents cover all future uses simplifies administrative work but creates legal exposure.
Prevention: Require separate written authorization specifically stating:
- The patient’s name and date of birth
- Specific statement that the patient authorizes sharing PHI on social media
- Named platforms (Facebook, Instagram, LinkedIn, TikTok, etc.) where content will appear
- Specific description of the information authorized for sharing
- Time period for which authorization is valid
- A clear statement that authorization can be revoked at any time in writing
4. Inadequate Approval Workflows for Content Review
Many healthcare organizations lack formal content approval processes for social media. Marketing teams post content with minimal review, or compliance review occurs only after publication—too late to prevent violations. Without documented approval workflows, organizations cannot prove they attempted to prevent violations when OCR investigates incidents.
The Violation: Publishing healthcare social media content without documented compliance review and approval before publication.
Why It Happens: Social media moves at speed. Formal approval processes feel slow and bureaucratic compared to the agility that social platforms demand. Teams often rationalize that they will “get approval later” or assume marketing has adequately reviewed compliance.
Prevention: Establish and document formal approval workflows that include:
- Clinical/Compliance Review: At least one person with healthcare compliance training reviews all patient content before publication
- Patient Authorization Verification: Designated team member confirms written authorization exists for any PHI-related content
- Audit Trail Documentation: Maintain records showing who approved content, when approval occurred, and what was approved
- Escalation Process: Define procedures for flagging content that requires special review
- Training Requirements: All staff handling patient content complete annual HIPAA social media training
5. Inadequate Patient Consent Documentation Systems
Even when patients provide authorization, many healthcare organizations fail to maintain organized records of that authorization. When OCR investigates violations, organizations cannot quickly locate or verify that proper consent existed. This documentation failure transforms a compliant posting into an apparent violation because the organization cannot demonstrate compliance.
The Violation: Lacking documented records proving patient authorization for specific social media use.
Why It Happens: Authorization forms are collected across multiple departments and stored in various locations. Without centralized systems, organizations lose track of which patients authorized which uses. When social media problems arise, organizations cannot quickly locate supporting documentation.
Prevention: Implement centralized authorization tracking systems:
- Single Accessible Repository: All patient authorization documents stored in one secure, searchable system.
- Link to Published Content: Tag published posts with authorization document references.
- Version Control: Track authorization form updates and maintain all versions.
- Expiration Tracking: Monitor authorization expiration dates.
- Audit Access: Maintain logs of who accesses patient authorization records.
- Regular Reconciliation: Quarterly audit of published patient content against authorization records.
6. Using Patients’ Real Names Without Proper Authorization
Some healthcare organizations believe that sharing a patient’s first name only constitutes sufficient privacy protection. This misses the point that HIPAA protects identifiability, not just specific identifiers. In small communities or specific circumstances, even first names combined with diagnosis or age can identify individuals.
The Violation: Publishing identifying information that, combined with available public information, allows identification of the patient.
Why It Happens: Using real names personalizes stories and increases patient recognition. Teams assume that omitting last names provides sufficient privacy, not recognizing that HIPAA regulates identifiable information regardless of completeness.
Prevention: Require policy compliance with either:
- Use only initials or completely anonymized identifiers. (“Patient M,” “Our recent transplant recipient”)
- Remove all real names from content unless specific written authorization explicitly authorizes naming the patient.
- Conduct a de-identification review before publication using the HIPAA Safe Harbor standard.
7. Oversight of Third-Party Social Media Tools Lacking HIPAA Compliance
Healthcare organizations frequently use standard social media management platforms to schedule and manage posts. Many of these platforms lack Business Associate Agreements and HIPAA compliance certifications. When organizations input PHI into non-compliant tools, they violate HIPAA even if the content never reaches the public.
The Violation: Transmitting or storing PHI using third-party tools that lack HIPAA compliance and Business Associate Agreements.
Why It Happens: Commercial social media tools offer features and convenience that custom-built solutions cannot match. Healthcare marketing teams adopt these tools without compliance vetting, focusing on functionality rather than regulatory requirements.
Prevention: Establish tool evaluation and vetting procedures:
- BAA Verification: Require Business Associate Agreements before using any tool that processes patient data.
- HIPAA Compliance Assessment: Verify the vendor maintains HIPAA compliance through independent audits.
- Alternative Workflows: For non-compliant tools, ensure PHI never enters those systems
- Vendor Management: Maintain current vendor agreements and compliance documentation.
- Staff Training: Ensure all team members understand which tools are compliant.
Stop Compliance Violations With Automated Social Media Review Workflows
ContentBridge’s healthcare-focused compliance features flag risky content before publication and maintain complete audit trails for regulatory investigations.
Your Step-by-Step HIPAA Compliance Process for Social Media
Preventing HIPAA violations requires systematic processes that become routine rather than exceptional. This five-step framework transforms social media compliance into standard operating procedure.
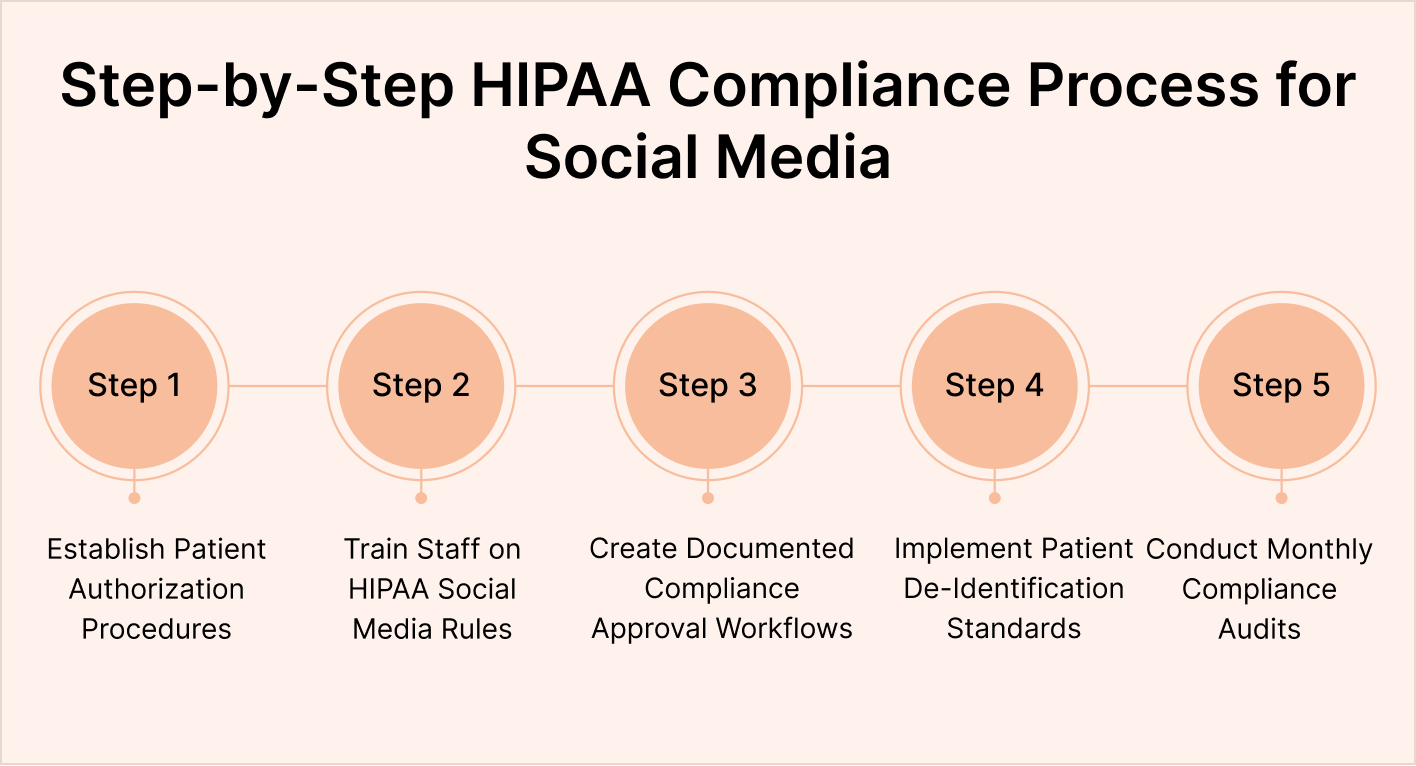
Step 1: Establish Written Authorization Procedures and Documentation Systems
Begin by creating standardized authorization forms that specifically address social media use. The form must clearly explain what social media is, name the specific platforms where content will appear, and state exactly what type of information will be shared. Have your healthcare legal team or compliance officer review the form to ensure it meets HIPAA requirements.
Implement a centralized system for collecting and storing authorization documents. This system should allow staff to quickly verify that authorization exists before content publication. Without centralization, authorization documents disappear into various filing systems and become impossible to locate when needed.
You can use a healthcare social media management platform like ContentBridge that helps maintain detailed audit trails for content authorization. This platform is tailored to healthcare social media workflows and helps ensure complete compliance and documentation.
Step 2: Train All Staff on HIPAA Social Media Requirements
Annual HIPAA training typically covers medical records protection, but often omits social media-specific compliance. Require specialized training that addresses:
- What constitutes PHI in the social media context
- How to recognize HIPAA violations in patient stories and photos
- Authorization procedures and documentation requirements
- De-identification techniques and the HIPAA Safe Harbor Method
- Approved versus prohibited types of content
- Procedures for reporting suspected violations
Train staff quarterly on compliance updates and share case studies of real OCR enforcement actions to demonstrate consequences. Make compliance tangible and meaningful rather than an abstract regulatory requirement.
Step 3: Create Approval Workflows That Document Compliance Review
Establish formal content approval processes that create audit trails for every published post. At a minimum, approval workflows should include:
- Content Creator Submission: Staff member drafts content and submits it through the designated system.
- Compliance Review: Designated compliance reviewer reviews for PHI and authorization.
- Authorization Verification: Second reviewer confirms written authorization exists for patient-related content.
- Final Approval: Marketing manager or senior leader approves content before publication.
- Publication and Documentation: System records approved content, approval dates, approving individuals, and authorization document references.
This workflow ensures no content reaches social media without a documented compliance review. The approval trail protects your organization by demonstrating good-faith compliance efforts if violations occur.
Step 4: Implement De-Identification Standards for Patient Stories
De-identification allows healthcare organizations to share compelling patient success stories while protecting privacy. The HIPAA Safe Harbor Method specifies that organizations can safely share information after removing these 18 identifiers:
- Patient names
- Geographic data smaller than the state (addresses, ZIP codes, city names combined with the state)
- Dates more precise than year (birth dates, admission dates, discharge dates)
- Telephone numbers and fax numbers
- Email addresses
- Social security numbers
- Medical record numbers
- Health plan account numbers
- Account and license numbers
- Postal addresses
- Vehicle identifiers (license plate numbers)
- Biometric identifiers and voice recordings
- Full face photos or comparable images
- Age greater than 89 years
- Employer names and employee identification numbers
- Dates of admission/discharge (exception: year only is permitted)
- Date of death
- Any other unique characteristics that could identify the individual
After removing these identifiers, your organization can freely share patient information on social media without authorization or HIPAA compliance concerns.
Step 5: Conduct Monthly Content Audits and Compliance Reviews
Monthly audits of published content ensure ongoing compliance and catch violations before OCR investigations. Audit procedures should include:
- Review all patient-related content published in the past month
- Verify that authorization documentation exists for each patient featured
- Confirm that de-identification procedures were followed appropriately
- Check that no additional identifiers were included in associated comments or responses
- Identify any potential risks for correction
- Document audit results and flag items requiring follow-up
Monthly audits transform compliance from a point-in-time concern into continuous risk management.
Best Practices for HIPAA-Compliant Patient Content
Beyond preventing violations, healthcare organizations can proactively build compliance excellence into social media operations.
1. Develop Written Social Media Governance Policies
Document your organization’s social media compliance standards in a written policy that all staff understand. The policy should cover:
- Types of patient content authorized for social media (success stories, testimonials, educational content)
- Prohibited content (specific diagnoses without authorization, graphic medical images, identifying information)
- Required approval processes and responsible parties
- Authorization procedures and documentation standards
- De-identification requirements when applicable
- Handling of patient comments and identifying information shared in post responses
- Consequences for policy violations
- Process for reporting suspected violations
Written policies demonstrate organizational commitment to compliance and provide clear guidance that reduces inadvertent violations.
2. Use HIPAA-Compliant Social Media Management Platforms
When selecting social media management tools, require HIPAA compliance and Business Associate Agreements. Compliant platforms provide features specifically designed for healthcare compliance:
- Content approval workflows with documented audit trails
- Authorization document storage and tracking
- De-identification checking and recommendations
- HIPAA-specific permission and role management
- Compliance reporting and audit capabilities
- Patient privacy controls and de-identification templates
3. Implement Role-Based Access and Permissions
Not all staff should have equal access to patient information or content publication capabilities. Implement role-based permissions:
- Clinical Staff: Can mark content as patient-appropriate for marketing use and indicate authorization status.
- Compliance Reviewer: Required reviewer on all patient-related content before publication.
- Marketing Team: Creates and submits content, but cannot unilaterally approve.
- Approver/Publisher: Final authority who confirms compliance before publication.
- Audit Staff: Can view all content and approval,s but cannot modify.
This role-based approach distributes responsibility and ensures multiple eyes review sensitive content.
Train on Real OCR Enforcement Actions
Make HIPAA compliance real by studying actual OCR enforcement actions involving healthcare social media. The Office for Civil Rights publishes settlement summaries detailing violations, investigation findings, and penalties. Review these cases with your team to understand what triggers investigations and how violations occur despite good intentions.
Turn HIPAA Guidelines into Built-In Social Media Workflows
ContentBridge helps healthcare teams standardize approvals, control access, and document consent so no post goes live without proper review.
Build a HIPAA-Safe Social Media System with ContentBridge
Preventing HIPAA violations on social media is not just about training your team once a year. It requires structured processes, documented consent management, controlled publishing access, and clear approval workflows.
Healthcare marketing teams often operate across multiple departments, facilities, and stakeholders. Without centralized oversight, the risk of accidental disclosure increases significantly. A single unauthorized post can lead to financial penalties, reputational damage, and loss of patient trust.
This tension dissolves when organizations implement systematic compliance processes with purpose-built technology. ContentBridge is a frontline-first social media management platform built specifically for healthcare compliance. The platform automates approval workflows, tracks patient authorization, flags risky content before publication, and maintains audit trails demonstrating compliance efforts.
How ContentBridge Helps Prevents HIPAA Violations on Social Media
Automated Approval Workflows: Compliance reviewers receive notifications for every patient-related post. Content never goes live without flowing through defined approval processes. Documented audit trails prove compliance efforts.
Authorization Tracking: A centralized system stores all patient authorization documents and links them to published content. Compliance officers quickly verify that authorization exists for any patient featured. Monthly reconciliation identifies authorization gaps before investigations occur.
Compliance Flagging: The platform identifies potentially risky content before publication. Posts containing suspected PHI, missing authorization, or prohibited identifiers receive compliance alerts. Staff can correct issues immediately rather than discovering problems after publication.
De-Identification Templates: Pre-built templates guide staff in removing identifiable information. De-identification recommendations appear as staff write content, providing real-time compliance guidance. This transforms de-identification from a complex regulatory concept into an actionable workflow step.
Audit Trail Documentation: Every approved post is documented with reviewer names, approval dates, authorization references, and content versions. When OCR investigates, your organization has complete documentation proving systematic compliance efforts.
Multi-Location Coordination: Healthcare systems managing social media across multiple locations face coordination challenges that multiply compliance risk. ContentBridge’s role-based permissions and centralized oversight ensure consistency across all locations. Local teams receive clear compliance guidance while corporate oversight prevents violations.
If your organization is serious about preventing HIPAA violations while maintaining an active, engaging social media presence, it’s time to move beyond basic tools.
Book a demo with ContentBridge today and see how you can manage hospital social media with confidence, control, and compliance.
Frequently Asked Questions
What happens if a hospital violates HIPAA on social media?
HIPAA violations investigated by the Office for Civil Rights trigger penalties starting at $100 per violation and escalating to $50,000+ per violation based on circumstances. Organizations also face investigation costs, remediation expenses, mandatory compliance programs, and reputational damage. Most significantly, organizations must notify affected patients, media outlets, and law enforcement within 60 days, creating public disclosure of the breach. Patient trust loss often exceeds financial penalties in long-term impact.
Can hospitals post patient photos on social media without written authorization?
No. Verbal permission is insufficient under HIPAA. Written authorization specifically addressing social media use is required. The authorization must explicitly state which platforms will receive the photo and that it will be shared with the general public. Generic consent forms covering treatment and privacy practices do not authorize social media photography.
Is de-identification the same as anonymization?
De-identification under HIPAA’s Safe Harbor Method is more specific than general anonymization. Safe Harbor de-identification requires the removal of 18 specific identifiers using a documented method. While anonymization is a broader concept that could use various approaches, HIPAA Safe Harbor provides a specific, legally safe method that organizations can use to share information without authorization or additional HIPAA compliance concerns.
Does patient consent for treatment authorize social media use?
No. Separate authorization specifically for social media use is required. Patient consent for treatment and privacy practices is limited to that healthcare relationship. HIPAA requires specific, documented authorization before any use or disclosure beyond the original treatment context. Social media publication is a distinct use requiring separate explicit consent.
What should healthcare organizations do if they discover they’ve posted HIPAA-violating content?
Immediately remove the violating content from social media, notify your compliance officer, and document the incident, including what was posted and for how long. Assess whether the violation constitutes a reportable breach under the HIPAA Breach Notification Rule (generally, breaches affecting more than 500 residents require notification to the media and HHS). Consult with healthcare legal counsel about notification obligations and potential OCR reporting. Implement corrective action to prevent recurrence. Many minor incidents that are promptly corrected do not escalate to formal OCR investigations.

