Your hospital marketing team posted a heartwarming story about a patient’s successful surgery recovery. The photo shows the smiling patient with medical staff in the recovery room. Then your compliance officer calls with bad news: the hospital name band is visible on the patient’s wrist in the background. The photo reveals which specific patient received what procedure on what date. The post violates HIPAA.
This scenario plays out at hospitals nationwide every single week. Hospital teams genuinely want to share patient success stories, educate communities about health conditions, and build trust through authentic experiences. The problem is not intent; it is that social media platforms, by design, expose data that healthcare organizations must protect. Patient names, medical details, photos, location information, and metadata all create breach risks that traditional safeguards miss. Recognizing the compliance risks of frontline social media is the first step toward preventing these exposures.
Protected health information (PHI) exposure on hospital social media triggers consequences far beyond simple mistakes. The Office for Civil Rights (OCR) has increased enforcement actions against healthcare organizations for social media PHI breaches. Federal fines start at $100 per violation and escalate to $50,000+ per occurrence. According to Verizon’s Data Breach Investigations Report 2025, human error causes 60% of healthcare breaches. Affected patients lose trust in your organization permanently. Competitors seize market share while your reputation recovers.
This guide explains exactly how hospitals can protect patient data on social media. You will learn which patient information creates breach risks, which safeguards actually prevent exposure, and how to implement workflows that transform social media from a compliance threat into a strategic asset. Whether you are responsible for hospital social media, compliance, information security, or patient engagement, this guide provides the complete framework needed to protect PHI while maintaining authentic patient connections.
The Patient Data Risks That Hospital Social Media Creates
Hospital social media creates multiple pathways for patient data exposure that traditional healthcare settings do not encounter. Understanding these risks helps you implement targeted protections that prevent breaches.
1. Background Patient Information in Photos and Videos
Hospital photos often contain accidental patient data exposure in the background. A recovery photo may include whiteboards listing medications. Videos might show patient names on clipboards or identification bands. Even careful composition reveals facility location, patient demographics, and specific procedures simultaneously. HIPAA violations occur from the background context that helps identify patients. Your hospital must review every image pixel by pixel before posting.
2. Metadata Exposure from Images and Location Tags
Photos contain invisible metadata that identifies locations, dates, times, and devices. A hospital selfie includes embedded GPS coordinates pinpointing the exact facility location and specific floor. When combined with employee social media profiles, metadata creates a detailed map of hospital operations. Metadata becomes dangerous when patients tag themselves, revealing their hospitalization to their followers. Metadata stripping tools are mandatory for healthcare social media safeguards.
3. Contextual Re-identification of De-identified Content
Hospitals often believe removing patient names creates safe content. However, de-identified data can be re-identified when combined with other publicly available information. A post about “a grateful patient who received heart surgery” seems safe until former colleagues, family members, or competitors piece together the patient’s identity from scattered demographic hints. Information harmless in isolation becomes identifying when combined with external knowledge.
4. Direct Messages Containing Patient Health Information
Patients increasingly reach out to hospital social media accounts with health questions and medical information. Hospital staff responds through direct messages, thinking private conversations are exempt from HIPAA. However, HIPAA protections extend to private communications containing patient health information. Direct message conversations create documentation gaps because social media platforms retain history, backups, and metadata. Hospitals must treat social media direct messages with the same protections as official medical records.
5. Employee Personal Accounts and Work Experiences
Hospital employees frequently share work experiences on personal social media without recognizing that they are disclosing PHI. A nurse posting “Just finished the most complicated appendectomy ever” with enough detail that a patient could be identified violates HIPAA on their personal account. This is one of several reasons the frontline teams’ social media passwords disaster occurs so frequently in healthcare. Hospitals must implement policies extending to employee personal accounts, require training on PHI, and establish consequences for violations.
Monitor Hospital Social Media for Patient Data Exposure
ContentBridge provides real-time monitoring that detects PHI breaches before they spread across social platforms. Automated alerts notify your team instantly of compliance risks.
18 HIPAA Identifiers Every Hospital Social Media Team Must Know
The HIPAA Privacy Rule defines 18 specific identifiers that must be removed for health information to be considered de-identified under the Safe Harbor method. If any of these identifiers are present alongside health information, the data becomes Protected Health Information (PHI) and cannot be shared without patient authorization. Hospital social media teams must understand every identifier to prevent compliance violations.
- Names: Full names, initials, or any name variations of the patient, their relatives, employers, or household members.
- Geographic data: All subdivisions smaller than a state, including street address, city, county, precinct, and zip code, except the first three digits of a zip code if the area contains more than 20,000 people.
- Dates: All elements of dates except year, including birth date, admission date, discharge date, date of death, and all ages over 89.
- Telephone numbers: Home, mobile, and any other telecommunications numbers associated with the individual.
- Fax numbers: All fax numbers linked to the patient or their household.
- Email addresses: All email addresses associated with the individual.
- Social Security numbers: Complete SSN or any portion of it.
- Medical record numbers: Any internal record identifiers assigned by healthcare providers.
- Health plan beneficiary numbers: Insurance or plan identifiers linked to the patient.
- Account numbers: Financial or administrative account numbers tied to the individual.
- Certificate or license numbers: Driver’s licenses, professional certifications, passports, or other issued credentials.
- Vehicle identifiers and serial numbers: Including VINs and license plate numbers visible in photos or videos.
- Device identifiers and serial numbers: Medical device identifiers that can pinpoint specific patients.
- Web URLs: Any web addresses linked to or identifying the individual.
- IP addresses: Internet Protocol addresses that can track location and identity.
- Biometric identifiers: Fingerprints, voiceprints, retinal scans, and similar biometric data.
- Full-face photographs and comparable images: Any photographic image that could identify the individual, not limited to face images.
- Any other unique identifying number, characteristic, or code: Any additional identifier that could be used alone or in combination to identify an individual.
These 18 identifiers do not exist in isolation. A single identifier may not re-identify a patient, but multiple identifiers combined create clear pathways to identification. Hospital social media teams that train every content creator to recognize these identifiers and screen for them systematically will prevent violations before they reach the public. For a step-by-step compliance workflow, explore how to ensure hospital posts are HIPAA compliant.
Prevent Patient Data Breaches on Hospital Social Media
ContentBridge identifies all 18 HIPAA identifiers automatically before posts reach your audience. Metadata stripping and content review workflows prevent accidental PHI exposure.
Technical Safeguards to Prevent Patient Data Breaches on Social Media
Technical safeguards must create barriers to PHI exposure at every stage where content is created, reviewed, and published. These protections must work reliably across all devices used by hospital staff.
1. Enforce Role-Based Access Control for Social Media Accounts
Unrestricted access means anyone can post sensitive information or compromise security. Role-based access control limits what each employee can do based on their position, ensuring drafters cannot publish independently, and reviewers cannot delete content.
Enforce RBAC through dedicated management platforms rather than relying on employee discipline. Without proper access controls, organizations face the kind of governance failures described in the risk of manual social media scheduling.
2. Automate Metadata Stripping Before Publication
Staff cannot reliably remove metadata from images manually, and GPS coordinates, timestamps, and device information embedded in photos create serious identification risks. Automated stripping should happen before staff see preview images, preventing accidental uploads with location or patient-identifying data intact.
3. Deploy Real-Time Content Monitoring for Accidental PHI
Real-time monitoring tools should scan every post before publication and flag potential HIPAA violations for human review. Natural language processing can identify patient names, conditions, medications, and exposure patterns like specific diagnoses combined with demographics or visible identifiers in images.
4. Require Multi-Factor Authentication on All Accounts
Unauthorized access to hospital social media accounts could lead to posting patient information or impersonating the organization. MFA prevents compromise even when passwords are weak and should be mandatory with no exceptions.
You can use ContentBridge, a healthcare social media management platform that offers built-in security features tailored to healthcare workflows. ContentBridge’s strong authentication guards prevent unauthorized access to your healthcare organization’s social media account.
5. Implement Audit Logging Across All Activity
Every action on hospital social media accounts should be logged with timestamps, user identification, and content details. Audit logs create accountability, support regulatory investigations, and help identify risky behavior patterns before they lead to a breach.
6. Secure Direct Messages and Private Communications
Patients frequently send health information through social media DMs, creating unprotected PHI outside secure systems. Implement automated responses redirecting patients to secure channels and establish protocols for immediately removing any PHI received through private messages.
Technical safeguards are only effective as a layered system. Hospitals that combine access controls, automated screening, monitoring, authentication, audit logging, and secure messaging will prevent breaches at every point of vulnerability.
How to Build Administrative Controls That Make HIPAA Compliance Second Nature
Technical safeguards fail without administrative processes that make compliance easier than non-compliance. When administrative controls are strong, sharing patient stories that build community trust becomes a safe and repeatable process rather than a compliance risk. Effective controls integrate protection into everyday workflows, so safeguarding patient data becomes the natural path.
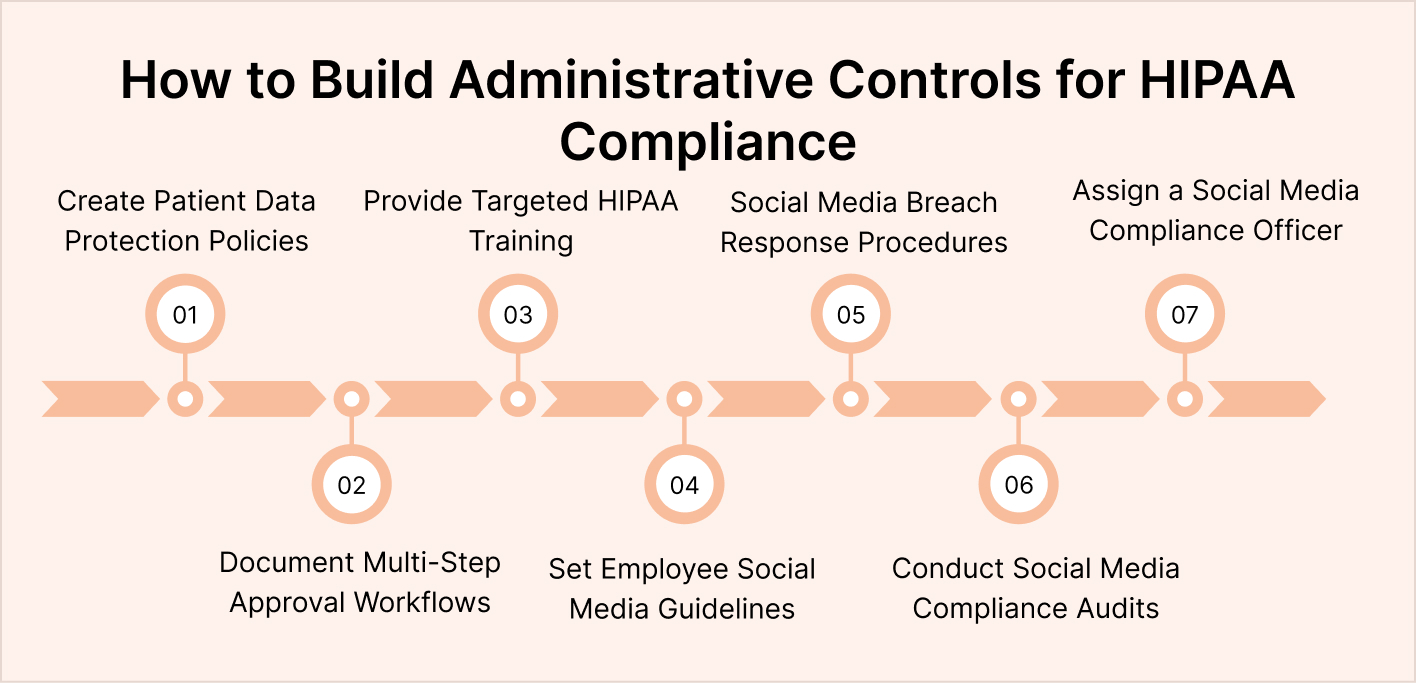
Step 1. Create Written Social Media Policies for Patient Data Protection
Policies must specifically address metadata, background information in photos, de-identification limits, direct message handling, and employee personal account restrictions. Staff should understand that a single careless mistake can trigger federal investigations and organizational fines. Building structured programs that let staff share content while protecting patient data creates the safeguards that make participation both possible and safe.
Step 2. Document Approval Workflows With Multi-Step Review
Require multiple reviewers before content reaches social media, with a creator drafting, a compliance reviewer flagging potential PHI, and a supervisor approving the final version. Documented workflows create accountability and demonstrate compliance efforts to OCR, and they are the primary mechanism for preventing HIPAA violations before patient content is posted. Without this structure, social media approval failure frontline teams experience leaves dangerous compliance gaps.
Step 3. Deliver Targeted Training Beyond Annual HIPAA Refreshers
Employees with social media access need training specific to patient data exposure risks, including case studies of actual breaches and real-world metadata examples. Training should be required annually with documented attestation before accessing any accounts.
Without proper training frameworks, compliance concerns increase and fear stops brands from letting frontline staff post, limiting the ability of hospitals to share authentic frontline stories safely.
Step 4. Establish Clear Employee Personal Account Guidelines
Staff often mention their workplace on personal social media, creating unintentional PHI exposure. Policies should define what employees can and cannot share about work, patients, and facilities, with specific examples of common violations.
Step 5. Define Incident Response Procedures for Social Media Breaches
Every hospital needs a documented response plan covering who to notify, how to remove content, and how to report incidents to OCR. Fast, structured response reduces regulatory penalties and demonstrates compliance commitment.
Step 6. Conduct Regular Compliance Audits of Published Content
Schedule quarterly audits of published social media content to identify PHI exposure, outdated claims, or posts that no longer meet compliance standards. Document findings and corrective actions as proof of ongoing diligence.
Step 7. Assign a Dedicated Social Media Compliance Officer
Designate a specific team member responsible for overseeing all social media compliance activities from policy enforcement to audit coordination. A single point of accountability prevents compliance from falling through departmental cracks and helps organizations avoid risks highlighted in why no social media is a risky compliance decision.
Hospitals that combine clear policies, documented workflows, targeted training, and ongoing accountability create a culture where protecting patient data is the default behavior, not the exception. A strong healthcare social media management programme ties all of these controls together into a single, auditable system.
Implement Healthcare-Specific Social Media Compliance Controls
ContentBridge provides training tracking, approval workflows, and documented controls designed specifically for healthcare teams managing patient data on social media platforms.
How to Create a Social Media Risk Assessment for Patient Data
Hospitals cannot implement effective safeguards without understanding their specific risks. Risk assessments identify which activities create patient data exposure, who has access to sensitive systems, and which safeguards currently exist. Healthcare organizations account for a significant share of all data breaches, making comprehensive risk assessment essential for any hospital launching or expanding social media programs.
- Inventory all social media accounts across platforms and departments: Identify who has access to each account, what content restrictions exist, and which accounts handle patient-specific information.
- Evaluate whether shared accounts exist without proper access controls: Credential management systems should prevent unauthorized access, and every account should have clearly documented ownership.
- Assess current content review processes end-to-end: Follow a post through the approval workflow from creation to publication, and time how long each step takes to identify where pressure to skip steps exists.
- Interview staff about their understanding of patient data risks: Observe actual workflows rather than assuming documented procedures are followed, and assess whether employees feel confident identifying potential HIPAA violations.
- Check technical controls, including multi-factor authentication and metadata stripping: Test whether employees can easily access patient information when creating content and whether safeguards prevent accidental exposure.
- Evaluate each platform’s native security controls: Document which social media platforms the organization uses and whether their built-in features meet hospital security requirements.
- Identify whether patients can tag themselves in hospital posts: Assess how user-generated content, comments, and direct messages containing patient information are monitored and handled.
- Review employee training quality and enforcement consistency: Evaluate whether non-compliance consequences are enforced equally across departments and whether training is updated regularly.
- Document all findings and create action plans for identified gaps: Risk assessments should be updated annually and whenever social media operations change significantly.
Documented risk assessments protect hospitals if OCR investigates breaches by demonstrating that leadership took reasonable steps to identify and address vulnerabilities. Hospitals that treat risk assessment as an ongoing process rather than a one-time exercise will stay ahead of emerging threats and maintain stronger compliance across every social media channel.
What to Do When Patient Data Is Exposed on Hospital Social Media?
Despite best efforts, patient data exposure occasionally occurs on hospital social media. Incident response procedures determine whether breaches receive contained remediation or escalate into federal investigations. Hospitals must prepare protocols before breaches occur.
Detect and Contain the Exposure Immediately
Every employee should know how to report suspected breaches, whether detected through automated monitoring, staff reports, or patient alerts. Remove or hide offending content immediately while documenting what was posted, when, and on which platform. Never delete permanently, as OCR may require preserved evidence.
Assess Breach Scope and Severity Quickly
Determine what patient information was exposed, how many patients were affected, and how long the content was visible. Severity assessment drives regulatory obligation, as HIPAA requires breach notification within 60 days if exposure exceeds a low probability of unauthorized access.
Fulfill Notification Obligations Without Delay
If unauthorized access occurred, notify affected patients within 60 days, describing what was exposed, how the breach happened, and what remediation steps are underway. Hospitals must also notify the media if the breach affects 500 or more individuals and report the incident to OCR.
Document Every Step for Regulatory Review
Maintain complete breach investigation documentation for at least six years, as OCR reviews these records during investigations. Thorough records covering timelines, decisions, and corrective actions demonstrate reasonable efforts and protect against escalated penalties. Organizations that lack this documentation often struggle with maintaining post approval audit trails.
Conduct a Post-Incident Review and Update Safeguards
After containment and notifications are complete, review what failed and why. Update policies, workflows, training, and technical safeguards based on lessons learned and share findings with your compliance committee to prevent recurrence.
A prepared incident response plan is the difference between a contained mistake and a regulatory crisis. Hospitals that establish clear protocols, train staff to act quickly, and document every step will minimize damage, maintain patient trust, and demonstrate the compliance commitment that regulators expect.
Detect Patient Data Breaches Before They Spread Across Social Media
ContentBridge provides automated breach detection and incident response documentation designed specifically for healthcare organizations required to comply with HIPAA breach notification requirements.
How ContentBridge Prevents Patient Data Breaches on Hospital Social Media
Patient data protection on hospital social media requires systems designed specifically for healthcare compliance. Generic social media management tools built for consumer brands cannot manage the complexity of HIPAA requirements. ContentBridge is a social media management platform built specifically to prevent patient data breaches through role-based access controls, automated metadata stripping, and real-time content monitoring that flags potential violations before content goes live.
Documented approval workflows create the compliance evidence that OCR requires during investigations. Reviewers flag patient data risks, track approval decisions, and make compliance boundaries explicit so staff understand exactly what they can and cannot post without relying on memory alone.
ContentBridge, a frontline social media management platform, generates compliance documentation automatically. Audit trails track account access, content posted, approval timestamps, and all changes made. This documentation demonstrates due diligence to OCR if breaches occur despite safeguards, proving your organization implemented reasonable protections.
Request a demo today to see how ContentBridge helps your hospital share meaningful content while preventing data breaches that damage patient trust and expose organizations to federal penalties.
Frequently Asked Questions
What patient data is protected by HIPAA on hospital social media?
HIPAA protects any individually identifiable health information on social media platforms, including patient names, medical conditions, treatment details, medications, appointment dates, photos, demographics, and any information that could reasonably identify a patient. De-identified content that removes names but contains enough context for re-identification also violates HIPAA. Content posted through direct messages containing health information is equally protected as official medical records.
Can a photo posted on a hospital’s social media reveal patient data accidentally?
Yes, photos commonly reveal patient data accidentally through background information, visible patient identifiers such as name bands or charts, and metadata containing GPS coordinates and timestamps. Even carefully composed photos often include whiteboards showing medications, clipboards displaying patient information, or facility details that identify which specific hospital departments treated patients. Metadata alone can pinpoint facility locations and specific floor information that combines with other details to identify individuals.
Why is metadata stripping mandatory for healthcare social media?
Metadata embedded in photos includes GPS coordinates, timestamps, device information, and cellular tower data that pinpoint exact locations and timing. Hospital staff posting photos may not realize their images contain location information. When combined with hospital name, department information, and employee social media profiles, metadata enables the identification of specific patients and procedures. Automated metadata stripping before publication eliminates this breach pathway.
How should hospitals manage direct messages containing health information?
Direct messages containing patient health information should be treated with the same protections as official medical records, including encryption and access controls. Hospitals should establish policies requiring that patient health questions be redirected to official patient portals rather than handled through social media direct messages. If conversations do occur through social media, they should be documented, encrypted, and maintained according to medical record retention requirements.
What written authorization do hospitals need before posting patient content?
HIPAA requires specific written authorization for each intended use of patient information. A patient’s consent to treatment does not imply consent for social media use. Hospitals must obtain separate, documented written permission specifically authorizing social media publication of patient information. Authorization should specify which platforms, whether content can be edited, the duration of authorization, and whether the patient has the right to request content removal.
What are the consequences of HIPAA violations on hospital social media?
HIPAA violations trigger federal investigations by the Office for Civil Rights, financial penalties starting at $100 per violation and escalating to $50,000+ per occurrence, mandatory notification of affected patients and media outlets, mandatory documentation of investigation and remediation, reputational damage, loss of patient trust, and potential civil lawsuits from affected patients. Enforcement actions increase significantly each year as OCR prioritizes healthcare social media compliance.

